Market Snapshot
Key Takeaways
Market Overview & Analysis
Report Summary
The global connected vehicle cybersecurity market is best understood as four interconnected spending pools rather than a single product category. In-vehicle protection covers ECU hardening, secure boot, in-vehicle intrusion detection and prevention systems (IDPS), network segmentation, CAN/Ethernet authentication, and hardware security modules. Secure OTA and software-update management covers cryptographic package signing, update orchestration, version control, software bill-of-materials (SBOM) management, and compliance with R156 and AIS-190-style mandates. Backend and fleet monitoring covers VSOC operations, cloud API protection, anomaly detection across vehicle fleets, mobile application security, threat intelligence sharing through Auto-ISAC and J-Auto-ISAC, and post-incident forensics. Secure hardware foundations cover HSMs, trust anchors, secure gateways, certificate management systems (PKI and KMS), and root-of-trust architectures that underpin all other security layers.
Regulatory mandates are the primary market-formation mechanism. UNECE R155 made CSMS certification a type-approval requirement in the EU, with mandatory dates of July 2022 (new vehicle types) and July 2024 (all new vehicles). Japan's AIS-189 became effective for new vehicle types from October 2025. India's AIS-189 equivalent has a phased implementation schedule. China's connected-vehicle cybersecurity framework is built around data governance, local storage, and export control measures published from July 2021, creating a distinct compliance environment for global OEMs operating there. The US BIS final rule of January 14, 2025, effective March 17, 2025, introduced the first hard supply-chain restrictions on jurisdiction-specific connected-vehicle technology, adding a geopolitical dimension to what was previously a purely technical compliance market.
The market's centre of gravity is shifting from compliance documentation to operational resilience. The first phase was proving CSMS and software-update processes for type approval. The current phase requires making those controls work at fleet scale across OTA delivery, telematics, mobile apps, cloud APIs, AI voice interfaces, EV charging links (including V2G attack surfaces), and supplier ecosystems spanning hundreds of ECUs and multiple tiers of supply chain. ISO/SAE 21434's lifecycle scope — from concept and development through production, operation, maintenance, and decommissioning — defines the full commercial footprint of cybersecurity spending across an OEM's programme lifecycle.
Market Dynamics
Key Drivers
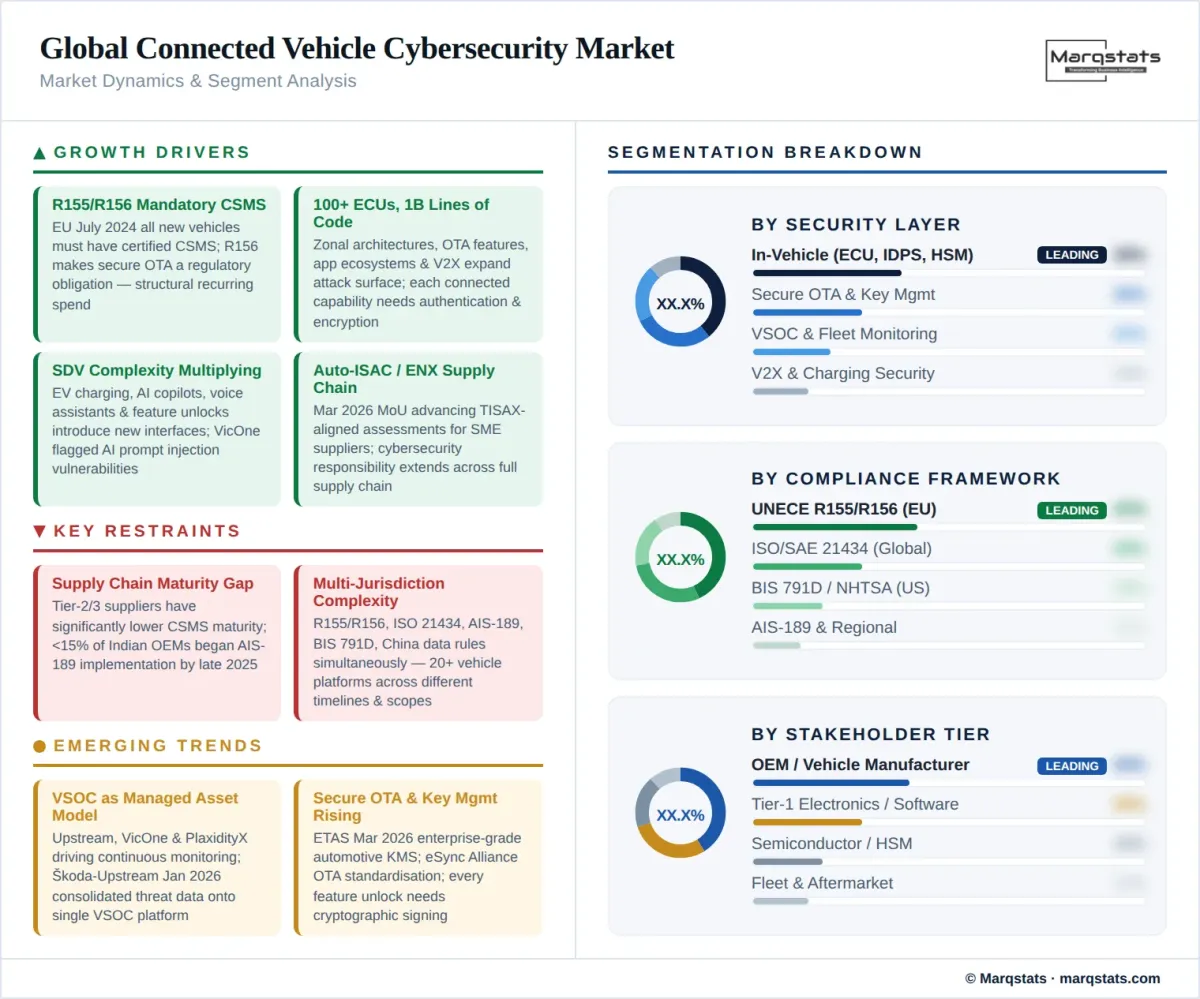
- UNECE R155/R156 mandatory CSMS and software-update governance as market foundation: The mandatory EU dates — July 2022 for new vehicle types and July 2024 for all new vehicles — have already forced broad OEM CSMS implementation in the world's most lucrative passenger-car market. R156's software-update management requirements have made secure OTA governance a regulatory obligation, creating a structural and recurring spending category that scales with the installed base of connected vehicles. NXP's automotive security framework and Infineon's ISO/SAE 21434-certified development process both reflect how deeply this regulatory mandate has penetrated the semiconductor and Tier-1 supplier layers.
- Software-defined vehicle complexity multiplying the ECU attack surface: Modern vehicles contain over 100 Electronic Control Units, with Level 5 autonomous vehicles estimated to require close to one billion lines of code. Zonal architectures, OTA-updatable feature sets, app ecosystems, and backend service orchestration expand the attack surface on every new platform generation. Each new connected capability — EV charging, V2X, AI copilots, voice assistants, over-the-air feature unlocks — introduces new interfaces that require authentication, encryption, and runtime monitoring. VicOne's 2025 reporting specifically flagged AI-related access vulnerabilities and prompt injection via voice assistants as emerging attack frontiers, signalling that cybersecurity spending will expand into AI model security and cloud model interfaces.
- BIS connected-vehicles rule creating a sovereign supply-chain compliance market: The January 2025 BIS final rule introduced restrictions on connected-vehicle software linked to entities with nexus in China or Russia, effective from model year 2027, and hardware restrictions from model year 2030. This has created an immediate market for supply-chain due diligence, component origin certification, architecture redesign to replace restricted sub-systems, and legal and technical advisory services. C2A Security's September 2025 partnership with HARMAN specifically cited the BIS US DoC 791D Rule as an addressable compliance challenge for carmakers and Tier-1 suppliers operating in the US market.
- V2X and EV charging infrastructure expanding the connected attack perimeter: Vehicle-to-Everything communication links — V2I, V2V, V2G, V2P — create bidirectional data flows between vehicles and public infrastructure with significant safety consequences if compromised. Bosch's November 2025 ConnRAD project results demonstrated that plausibility checks and hardware-based cellular authentication using hardware fingerprints are necessary to prevent malicious V2X data from being used for safety-critical vehicle functions. EV charging networks represent a distinct attack surface: AUTOCRYPT's November 2025 MENA expansion announcement highlighted its KMS, PKI, and charging station management cybersecurity systems as the foundation for securing EV charging infrastructure alongside vehicle security.
- Auto-ISAC, J-Auto-ISAC, and TISAX supply-chain hardening formalising collective defence: The March 2026 MoU between Auto-ISAC and ENX Association — the operator of the TISAX third-party cybersecurity assessment framework — creates a formal joint programme to advance supply-chain cybersecurity resilience, support scalable SME supplier assessments, and strengthen industry readiness. JAMA and JAPIA's 2025 cybersecurity guidelines explicitly aim to raise security levels across supply-chain participants of all sizes. These industry coordination mechanisms signal that the market has moved beyond OEM self-sufficiency toward a collective defence architecture where the entire supply chain must meet a rising baseline.
Key Restraints
- Supply-chain cybersecurity maturity gap at Tier-2 and Tier-3 levels: NHTSA's best practices and JAMA/JAPIA guidelines both explicitly place cybersecurity responsibility across the supply chain, but Tier-2 and Tier-3 suppliers — many of them SMEs — have significantly lower CSMS maturity than OEMs and large Tier-1s. By late 2025, fewer than 15% of Indian OEMs had begun serious AIS-189 implementation; a parallel readiness gap exists in the global supply chain. The Auto-ISAC/ENX MoU's focus on SME supplier scalability is a direct acknowledgement that this gap is the market's most critical unresolved execution risk.
- Regulatory fragmentation creating multi-jurisdiction compliance complexity: OEMs must simultaneously address UNECE R155/R156 (EU and aligned markets), ISO/SAE 21434 (global engineering standard), AIS-189 (India), BIS 791D (US), China's data-governance measures, and emerging frameworks in Japan, Korea, and other markets. Each jurisdiction has different timelines, scope, and technical requirements. For global OEMs managing twenty or more vehicle platforms across these markets, cybersecurity compliance is a multi-year programme management challenge, not a single regulatory checklist.
- Cybersecurity skills shortage constraining implementation velocity: Automotive cybersecurity requires a rare combination of embedded systems expertise, cryptographic knowledge, automotive protocols (CAN, Ethernet, AUTOSAR), cloud security, and regulatory fluency. The global shortage of qualified automotive cybersecurity engineers is a binding constraint on how fast OEMs and suppliers can implement CSMS, conduct TARA (Threat Analysis and Risk Assessment), and maintain VSOCs at the scale and sophistication required by R155 and ISO/SAE 21434.
Key Trends
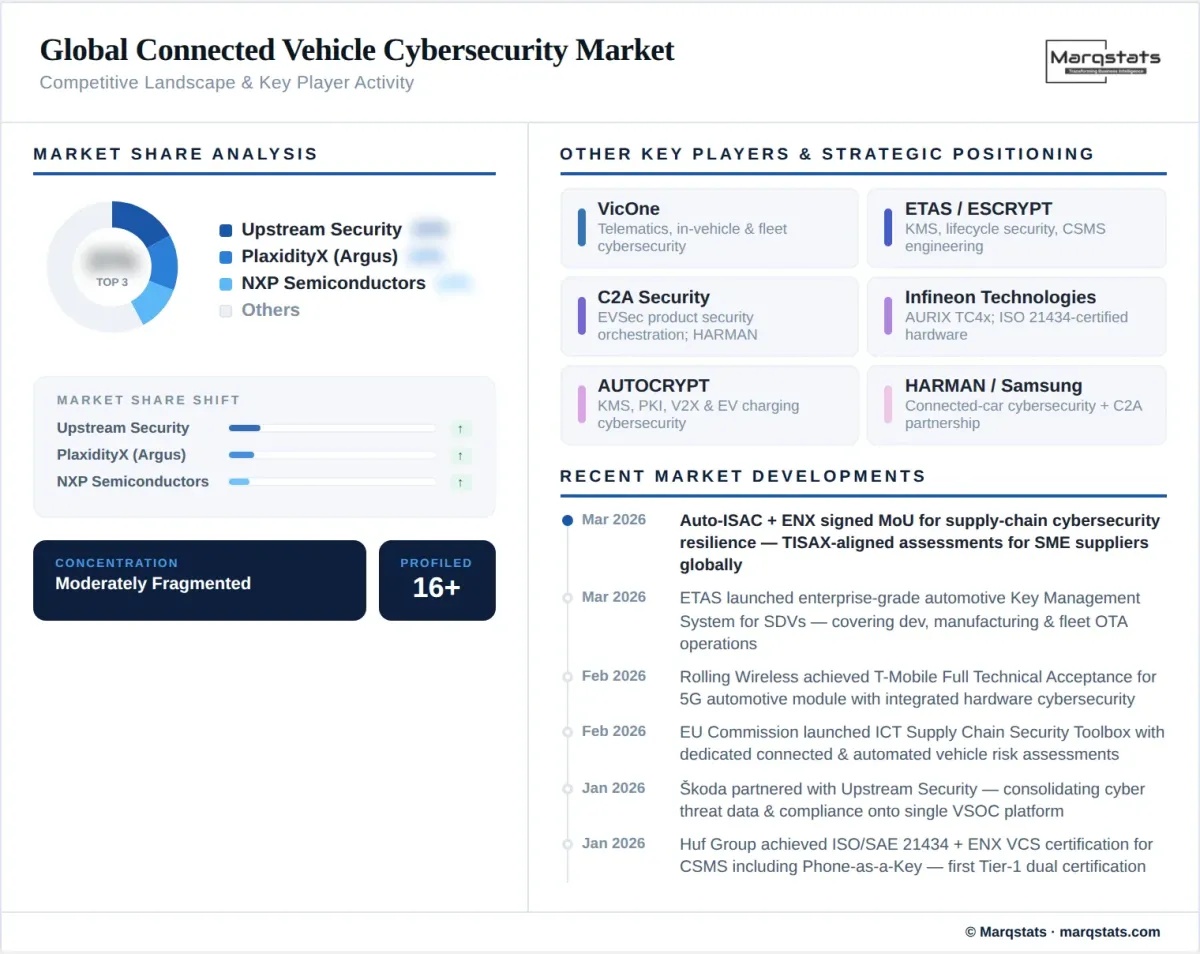
- VSOC adoption accelerating as connected vehicles become managed assets: The growth of Vehicle Security Operations Center offerings from Upstream Security, VicOne, and PlaxidityX reflects a fundamental shift in how OEMs conceptualise post-sale vehicle management. A connected vehicle is no longer a sealed product that leaves the factory and receives no further security attention; it is a managed asset requiring continuous threat monitoring, anomaly detection, incident triage, and remote response capability. Škoda's January 2026 partnership with Upstream Security — consolidating cyber threat data, risk insights, and compliance documentation into a single shared platform — is an illustration of how VSOC capabilities are moving from specialist security teams into mainstream OEM operations.
- Secure OTA and key management emerging as fastest-rising technical spending area: R156, ETAS's March 2026 launch of an enterprise-grade automotive Key Management System for software-defined vehicles, and the eSync Alliance's standardisation of OTA update and data management for automotive electronics (Tessolve's October 2025 membership) all point to OTA security and key lifecycle management as a rapidly growing technical sub-market. Every feature update, security patch, and software-defined feature unlock requires cryptographic signing, identity verification, anti-rollback protection, and auditability — creating a recurring operational spending requirement that scales with the OTA-updatable vehicle installed base.
- AI-related vulnerabilities and voice assistants emerging as new attack frontiers: VicOne's 2025 reporting explicitly flagged AI-related access and data vulnerabilities as an emerging cybersecurity spending category, specifically calling out voice assistants as targets for prompt injection attacks. As AI copilots, voice-controlled in-vehicle systems, and model-connected features proliferate across mass-market vehicles, cybersecurity will need to extend from ECU-level hardware protection into AI model security, inference-time input validation, and cloud model API authentication — representing a new wave of spending beyond the current embedded-security and CSMS market.
- EV powertrain and V2G cybersecurity becoming safety-critical, not just data-privacy concerns: Researchers have demonstrated that attacks on motor controllers via compromised CAN communications or malicious firmware can produce physical effects including unexpected acceleration, torque alteration, and inverter interference. V2G bidirectional power flows create a pathway from the grid to the vehicle's power electronics that introduces safety-critical cyber-physical risk beyond conventional data security. Leapmotor's November 2025 Security and Safety Lab in Hangzhou — integrating cybersecurity, data security, functional safety, and intended functional safety into a unified five-part framework — reflects how the industry is converging cyber and physical safety governance at the product level.
Market Segmentation
In-vehicle security — covering ECU hardening, secure boot, hardware security modules (HSMs), in-vehicle intrusion detection and prevention systems, CAN/Ethernet network segmentation, and domain controller security — is the foundational and largest revenue segment. It encompasses the security silicon embedded in every connected vehicle platform, making semiconductor suppliers NXP (4+1 layer secure vehicle architecture), Infineon (ISO/SAE 21434-certified AURIX TC4x family), and STMicroelectronics central to market economics. HARMAN's September 2025 partnership with C2A Security — combining the EVSec product security orchestration platform with HARMAN's cybersecurity engineering services — illustrates how Tier-1 electronics suppliers are building CSMS capability as part of their connected-car platform value proposition.
The secure OTA and software-update management segment is growing fastest by revenue, driven by R156 compliance obligations, the proliferation of OTA-updatable vehicle features, and the security requirements associated with software-defined vehicle architectures. ETAS/ESCRYPT's March 2026 launch of an enterprise-grade automotive Key Management System — covering secure key handling across development, manufacturing, and fleet operations including OTA software signing and certificate management — positions ETAS as a leading pure-play in this segment. The eSync Alliance's three-tier server-client-agent architecture for standardised OTA and data management, adopted by Tessolve in October 2025, represents the industry's move toward interoperable OTA security infrastructure.
Backend and fleet monitoring — encompassing VSOC operations, cloud API protection, mobile application security, fleet-level anomaly detection, and threat intelligence sharing — is the most strategically contested segment, as it creates the recurring managed-service revenue model that subscription-based cybersecurity vendors are competing to capture. Upstream Security's partnerships with Škoda (January 2026) and Auto-ISAC (October 2025) position it as a leading cloud-native fleet monitoring platform. PlaxidityX's March 2025 partnership with Deloitte Spain for an AI-driven VSOC represents the managed-detection-and-response model where cybersecurity consultancies and specialist vendors combine to deliver post-deployment fleet security operations.
Secure hardware foundations — HSMs, secure gateways, root-of-trust architectures, and PKI/KMS infrastructure — are a critical enabling layer whose commercial significance is often underestimated in market surveys focused on software and services. Without hardware-anchored cryptographic keys, secure boot, and hardware-enforced isolation, software-layer security controls are fundamentally incomplete. AUTOCRYPT's KMS and PKI technologies, expanded to MENA in 2026, and Infineon's hardware security concepts developed in the ConnRAD project — using inherent hardware signatures as cellular-communication fingerprints for V2X authentication — both reflect the security-by-hardware-design principle that the market is increasingly adopting.
Passenger vehicles account for the largest revenue share within connected vehicle cybersecurity, driven by the scale of OEM production volumes subject to UNECE R155/R156 in Europe, AIS-189 in India, and equivalent frameworks in Japan and other markets. The EU's mandatory July 2024 date for all new vehicles ensures that every passenger car sold in the EU must now come from a CSMS-certified OEM with a validated update management process. Rolling Wireless's February 2026 announcement of Full Technical Acceptance from T-Mobile for its RN932V 5G automotive module — featuring an integrated hardware cybersecurity engine — illustrates how next-generation vehicle connectivity hardware is being designed with security as an embedded component rather than an aftermarket addition.
Commercial vehicle and fleet cybersecurity is growing rapidly, driven by the expansion of OEM-embedded telematics platforms (Tata Fleet Edge, BharatBenz Truckonnect, Eicher My Eicher), ADAS safety system mandates that add safety-critical network interfaces, and the AIS-189/R155 compliance requirements that apply equally to M and N category vehicles. The ETAS India-ARAI MoU (July 2025) — creating tailored training programmes and certification courses for India's automotive industry including commercial vehicle OEMs, Tier-1 suppliers, and startups — reflects the emerging CV-specific cybersecurity capability-building market in growth economies.
EV charging infrastructure cybersecurity — covering charging station management security, ISO 15118 and OCPP communication authentication, V2G bidirectional power-flow security, and mutual authentication between vehicles and charging networks — is the fastest-growing emerging application, driven by the exponential expansion of public and private charging networks globally. AUTOCRYPT's dedicated CSMS for the connected mobility ecosystem, including KMS and PKI for charging infrastructure, and the EU Commission's February 2026 ICT supply chain security toolbox specifically including a risk assessment on connected and automated vehicles both signal regulatory and commercial acceleration of this sub-market.
By Geography
Europe
Europe is the world's most mature connected vehicle cybersecurity market, driven by mandatory UNECE R155 compliance from July 2024 for all new vehicles and the embedded role of ENISA, the EU Cybersecurity Agency, in shaping automotive cybersecurity standards. The February 2026 EU Commission ICT Supply Chain Security Toolbox — including a dedicated risk assessment on connected and automated vehicles — signals that automotive cybersecurity is moving into the EU's critical infrastructure protection framework, raising the regulatory bar further. TISAX, operated by ENX Association, has become the dominant third-party cybersecurity assessment framework for EU automotive supply chains, with its March 2026 MoU with Auto-ISAC extending its reach to North American supply chain participants. Germany is the technical and commercial centre, hosting Bosch's ConnRAD project (V2X security and resilience), ETAS/ESCRYPT's KMS and lifecycle security platforms, Huf's ISO/SAE 21434 and ENX VCS certification (January 2026), and the Sino-German autonomous connected driving cooperation dialogue.
North America
North America's connected vehicle cybersecurity market is being reshaped by two forces simultaneously: NHTSA's voluntary best-practice framework (still non-binding) and the BIS connected-vehicles final rule (effective March 2025) which introduced the first hard supply-chain restrictions on jurisdiction-specific CV technology. The BIS MY2027 software and MY2030 hardware restrictions are creating an immediate advisory, redesign, and compliance services market for OEMs and Tier-1s with China-linked supply chain exposure. Auto-ISAC's April 2025 updated Best Practice Guides and its October 2025 threat-landscape visibility partnership with Upstream Security, alongside the March 2026 MoU with ENX Association, position the US as an increasingly active industry coordination environment even in the absence of binding federal cyber regulation. The HARMAN-C2A Security partnership (September 2025) specifically targeting BIS 791D compliance services for carmakers reflects how the BIS rule is creating a new commercial sub-market.
Asia-Pacific
Asia-Pacific is the fastest-growing connected vehicle cybersecurity region, anchored by three distinct regulatory environments. Japan's AIS-189 (effective October 2025 for new vehicle types) and J-Auto-ISAC's 2024 collaboration with Auto-ISAC on emerging threat information sharing are building Japan's cybersecurity infrastructure alongside its broader software-defined vehicle investments. India's AIS-189 phased implementation — from 2025 for OEM CSMS governance to 2026–2027 for type-approval integration — is creating a large Tier-1 and OEM compliance services market; ETAS India's MoU with ARAI (July 2025) for tailored training programmes and the L&T Technology Services multi-year automotive cybersecurity engagement (January 2026) are early indicators of this market's scale. China's data-governance-heavy model, with multiple data-security measures for the connected-vehicle industry published from July 2021, creates a distinct compliance environment for foreign OEMs balancing global R155 obligations against China's local data storage and export control requirements.
Middle East, Africa, and Rest of World
The MENA region is emerging as a new connected vehicle cybersecurity market, driven by rapid EV infrastructure rollout, smart city initiatives, and a stated desire to adopt secure next-generation transportation technologies. AUTOCRYPT's November 2025 announcement of a dedicated 2026 MENA expansion — covering vehicle manufacturing, charging infrastructure, KMS, PKI, and CSMS — is the clearest commercial signal of this trend. The region's lack of an established local regulatory framework creates both an opportunity (first-mover advantage for cybersecurity platform vendors) and a challenge (absence of compliance-pull demand) compared with Europe and Asia. The EU's ICT supply chain security toolbox and border/customs security risk assessment suggest that supply-chain sovereignty concerns will increasingly influence cybersecurity requirements across connected-vehicle markets beyond the EU's borders.

How Competition Is Evolving
The global connected vehicle cybersecurity market is moderately fragmented, with competition structured across five distinct archetypes. Pure-play automotive cybersecurity platforms — Upstream Security, PlaxidityX (formerly Argus Cyber Security), VicOne, C2A Security, and AUTOCRYPT — compete primarily on cloud-native fleet monitoring, VSOC capabilities, CSMS automation, and regulatory evidence generation. Tier-1 automotive electronics suppliers — HARMAN, ETAS/ESCRYPT, Continental/AUMOVIO, and Bosch — embed cybersecurity as an integrated value layer within broader connected-car, SDV, and infotainment platforms. Semiconductor and secure-hardware providers — NXP, Infineon, STMicroelectronics, and Renesas — compete on HSM integration, secure-element design, and hardware root-of-trust architectures embedded in automotive SoCs and MCUs. Engineering services and testing specialists — LTTS, Tessolve, Ficosa, and KPIT — compete on CSMS implementation, TARA methodology delivery, ISO/SAE 21434 evidence generation, and Tier-1 integration services. Infrastructure and PKI/KMS specialists — AUTOCRYPT, ETAS (KMS), and Karamba Security — compete on certificate management, OTA signing infrastructure, and the cryptographic key lifecycle management that underpins the entire connected-vehicle security stack.
The market's most important structural trend is the convergence of in-vehicle security, secure OTA, and fleet monitoring into integrated platform offerings. Vendors offering only one layer — only in-vehicle IDPS, or only fleet analytics, or only OTA signing — face competitive pressure from platforms that can cover the full lifecycle from ECU-level hardware security through fleet-scale VSOC operations. VicOne's September 2025 partnership with Sasken enabling OEMs and Tier-1s to deploy cybersecurity across ECUs, operating systems, cloud systems, and charging infrastructure with audit-ready compliance evidence exemplifies this integration imperative. ETAS's March 2026 KMS launch, explicitly covering the full arc from development-time key generation through manufacturing and fleet OTA signing, similarly reflects the shift toward lifecycle-spanning platform offerings.
Companies Covered
The report profiles 16+ companies with full strategy and financials analysis, including:
Recent Market Activity
Table of Contents
Coverage & Segmentation
This report provides a comprehensive analysis of the global connected vehicle cybersecurity market covering the 2021–2030 period, with 2025 as the base year. The study examines the full cybersecurity value stack across four spending pools: in-vehicle protection (ECU security, secure boot, HSMs, IDPS, network segmentation), secure OTA and software-update management (R156 and AIS-190 compliance, SBOM management, cryptographic signing), backend and fleet monitoring (VSOC operations, threat intelligence, cloud API security, mobile app security, Auto-ISAC and J-Auto-ISAC participation), and secure hardware foundations (HSMs, PKI/KMS, secure gateways, root-of-trust architectures). Regulatory coverage spans UNECE R155 and R156, ISO/SAE 21434, BIS connected-vehicles final rule (March 2025), AIS-189 (India and Japan), China's data-governance measures, and emerging EV charging infrastructure standards including ISO 15118 and V2G security requirements. Geographic coverage spans Europe, North America, Asia-Pacific (Japan, China, India, South Korea), and emerging markets including MENA. This report covers passenger vehicles, commercial vehicles, and EV charging infrastructure; autonomous vehicle cybersecurity is addressed in a companion Marqstats report on the global ADAS and autonomous vehicle technology market.
Primary research included 40+ interviews with OEM cybersecurity programme directors, Tier-1 CSMS implementation leads, automotive cybersecurity platform vendors, VSOC operations managers, semiconductor security architects, and automotive regulatory advisors across Europe, North America, and Asia-Pacific. Secondary research drew from UNECE R155 and R156 official texts, NHTSA 2022 best practices, BIS connected-vehicles final rule documentation, Auto-ISAC Best Practice Guides, ISO/SAE 21434 and JAMA/JAPIA guidelines, EU Commission cybersecurity toolbox publications, and company press releases, investor presentations, and partnership announcements.